By far, remote access is one of the primary considerations of our clients in these times of rapid change. As a result, mass numbers of employees have been set up to connect remotely in some situations. The FFIEC IT Examination guidelines recommends employing the following measures (among others) to ensure security with regard to remote access:
- Tightly controlling remote access through management approvals and subsequent audits.
- Limiting the applications available for remote access.
Employing these recommendations during normal business operations is one thing, but how do you maintain tight control, continue audits, and keep track of who has access to remote applications when circumstances are frequently changing?
Permission Reviews for Remote Access
It’s a fairly common practice for organizations to enable remote access through a VPN in addition to using tokens as a way of establishing secure connections. Often, virtual desktop capability and other important applications are authenticated using Active Directory. Full access/permission reviews for all of Active Directory are common; however, when changes are happening so quickly, it’s not an ideal time to start an access/permission review for ALL of Active Directory. Still, many of our clients have security at the forefront of their minds. In fact, they were focused on making sure that potential risks weren’t introduced in the midst of so many changes.
One solution to reduce the risk while still maintaining a certain level of sanity is to consider permission reviews that are specific to remote access. This provides the ability to find any potential errors that may have been introduced and reduces the risk of improper access to critical systems.
To create reviews that are specific to remote access:
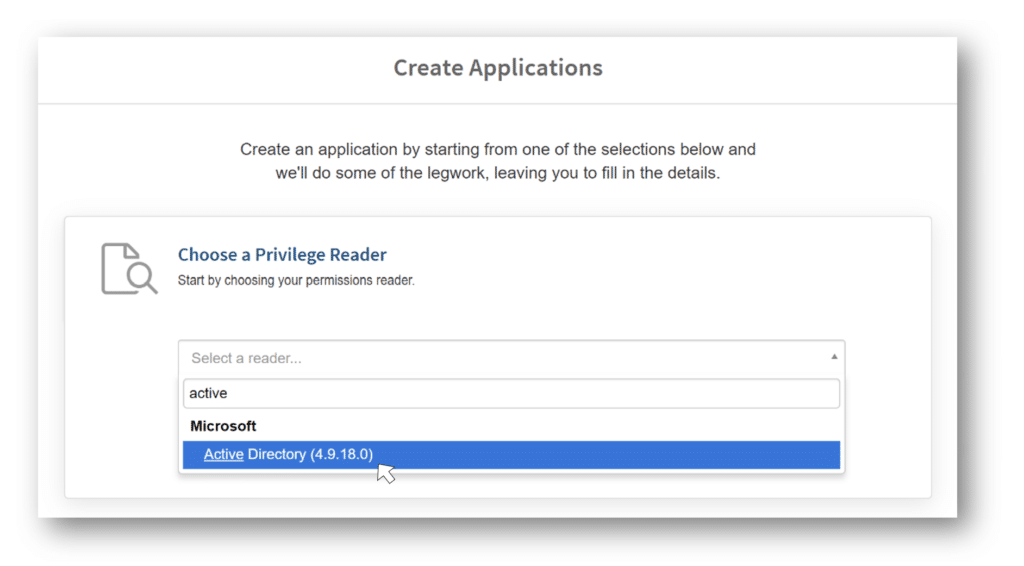
- Create a new application specifically for your remote access software using the Active Directory importer.
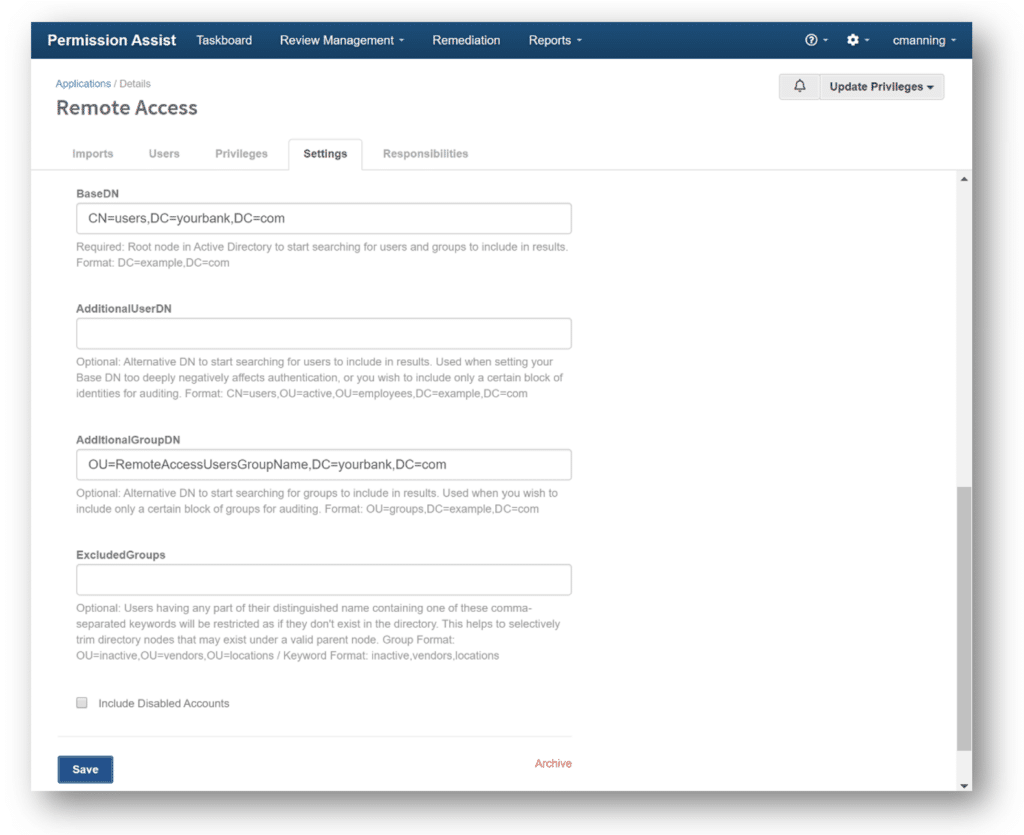
2. Specify the AD group employees need for remote access:
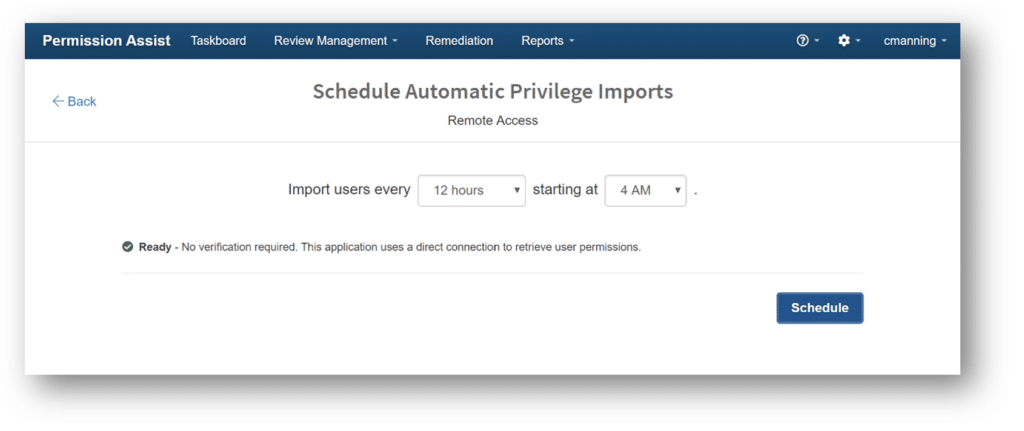
3. Schedule automatic imports – let Permission Assist handle the updates for you! New data can be imported weekly, daily, or multiple times a day. You just select the frequency and time that works best for you.
The application is ready for review! Creating a quick review specifically for your remote access application(s) saves time and helps you focus specifically on the changes.
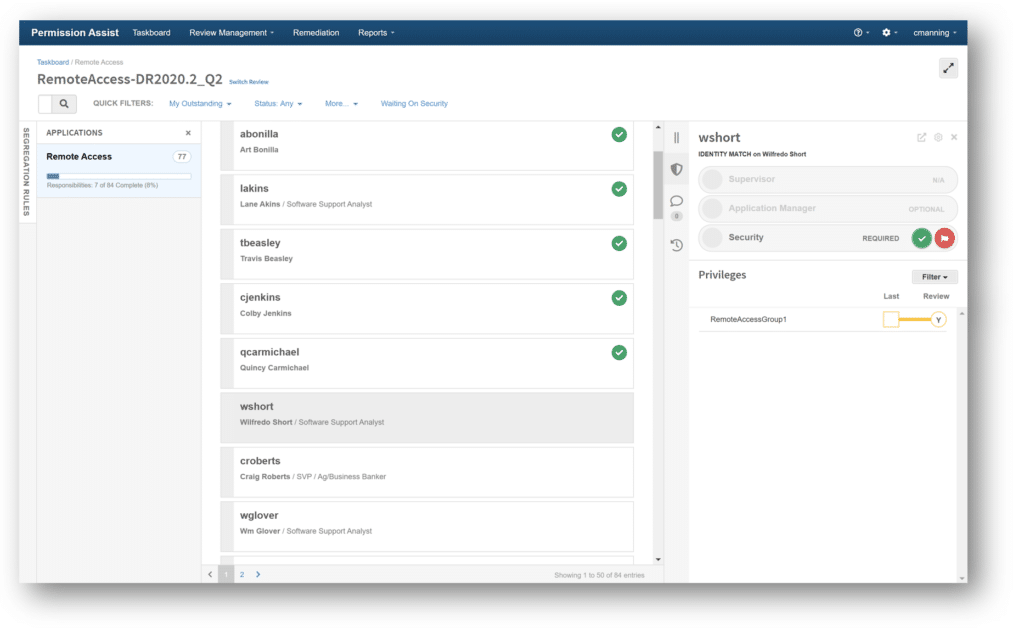
Tip: If you want to focus on your critical applications, create a review using the “Choose a Priority” option and select the “Critical” priority. Permission Assist will automatically include any applications identified as critical.
Tracking Added/Dropped Remote Access
Want a quick and easy way to track access outside of an official review? The Changelog allows you to quickly see whether access has been added, changed or removed.
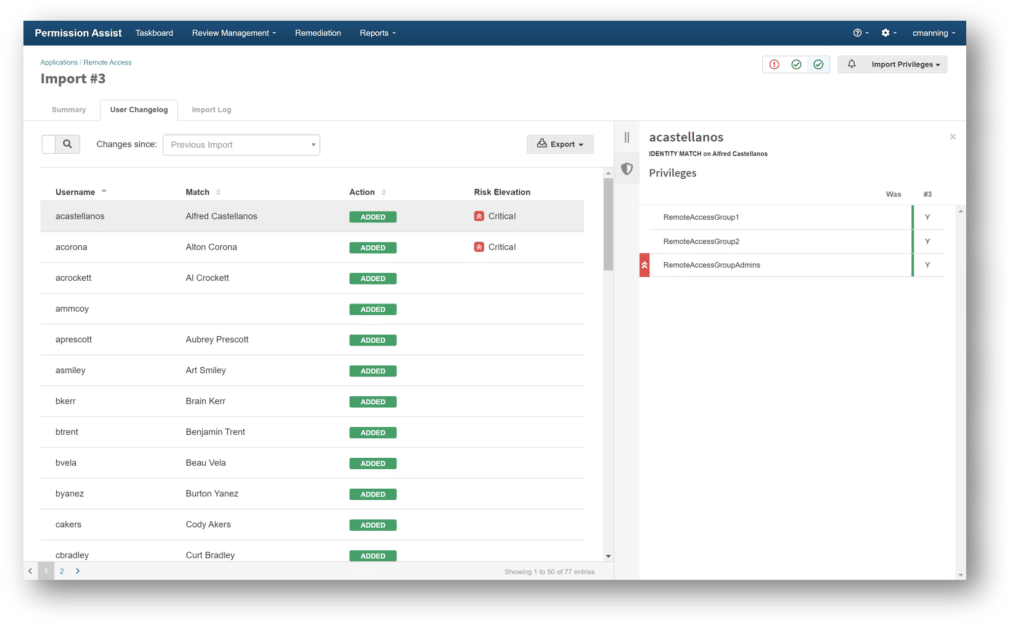
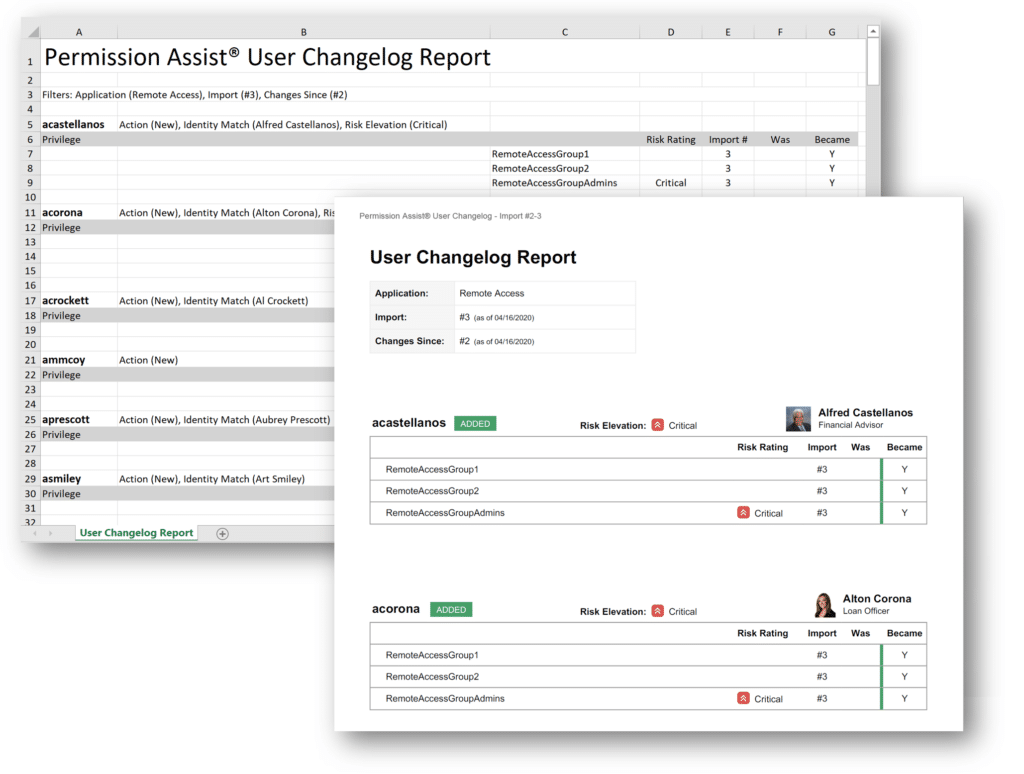
User Changelog data can be exported in either Excel or PDF format.
These are the moments you’ve planned for, and you’ve got this. We hope these tips help save some time and reduce stress.
Active Directory is a licensed trademark of Microsoft Corporation. All other product names, trademarks, registered trademarks, and service marks are property of their respective owners. All company, product and service names used in this website are for identification purposes only. Use of these names, trademarks and brands does not imply endorsement.